
WASP NEST DYNACON
Protect autonomous systems from cyber-attacks targeting control systems
About the project
|
|
Cyber-attacks targeting control systems, found in autonomous systems, are a relatively recent phenomenon. Unfortunately, it can have a devastating impact and harm both humans and the environment. In DYNACON four leading research groups in cyber physical security (control systems, real-time systems, communication and network security) at KTH, Lund University and Linköping University join forces to address the challenges of cyber-attacks in autonomous systems. |
The group will tackle issues such as false data and manipulation of timestamps. The idea is to use trusted embedded devices as well as cryptographic authentication when necessary. Also, they will look into how detection and observer schemes can be developed to handle attacks both in the local and the supervisory control.
Ongoing work 1: Sensor attacks on state estimation
Cyber-physical systems are systems that integrate computational and physical entities. Sensors play a key role in them by providing the critical data necessary for proper operation. Generally speaking, accurate sensors are more expensive, in terms of energy usage or time, compared to noisier and less accurate cheap sensors. In budget-constrained systems equipped with both types of sensors, one can balance measurement accuracy and costs by alternating between the cheap and expensive sensors according to a scheduling policy. Furthermore, expensive sensors often support authentication mechanisms, which reduces their vulnerability to tampering attacks, such as false data injection. Consequently, the expensive sensors’ readings could be exploited to reduce the impact of false data injection attacks.
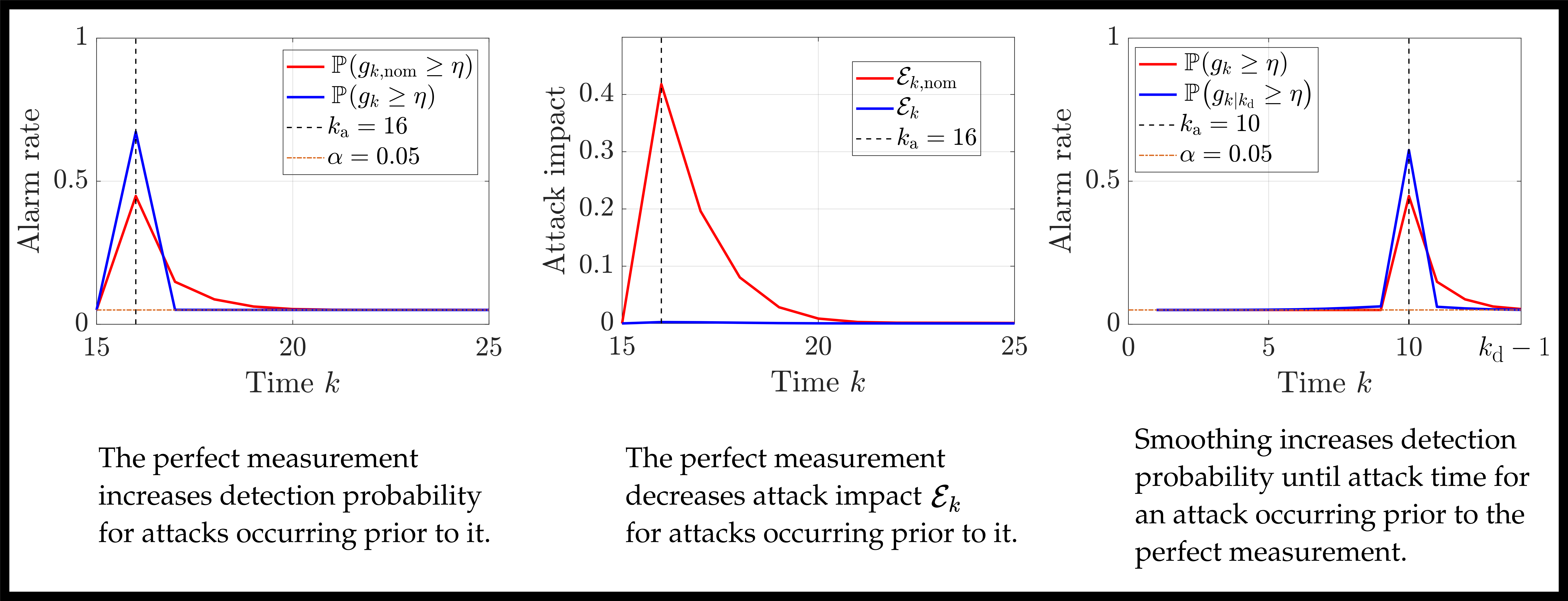
In this paper, we study how combining two such sensor types can enhance the security of state estimation in a discrete-time linear time-invariant (LTI) system subject to an additive sensor attack over a finite horizon. The system model features two measurement channels: a standard noisy measurement that is vulnerable to attack, and an intermittent noiseless full-state measurement — referred to as a perfect measurement — that is tamper-proof. A Kalman filter processes incoming measurements online, while a fixed-point smoother retrospectively refines past estimates once the perfect measurement becomes available. Attack detectability is assessed through static chi-squared hypothesis tests applied to three distinct detection statistics: one based on the standard Kalman filter innovation, one that directly compares the noisy and perfect measurements at the time they coincide, and one derived from the smoothed innovations.
We characterize analytically how the timing of the perfect measurement relative to the attack affects both estimation quality and detection probability. For attacks occurring after the perfect measurement, we show that the Kalman gain and innovation covariance are both reduced compared to a system relying solely on noisy measurements, meaning the attack degrades the state estimate less and is simultaneously easier to detect; both effects diminish monotonically as the attack moves further from the perfect measurement in time. For attacks occurring before the perfect measurement, retrospective smoothing improves detection probability at and before the attack time compared to the online Kalman filter statistic, but reduces it in the intermediate steps between the attack and the perfect measurement. This can be interpreted as a temporal redistribution of detection probability induced by smoothing, whereby dispersion across multiple time steps is traded for concentration at a single time step, thereby improving detectability. We further prove that smoothing anchored to a perfect measurement always yields a strictly higher detection probability at attack time than smoothing performed using only noisy measurements. These results are proven for the scalar case, and numerical experiments on a two-dimensional system suggest that the findings extend to higher-dimensional settings. The future work includes extending provably showing that the results indeed extend to the multi-dimensional case as well.
Researchers: Jacopo Porzio,
Rijad Alisic,
György Dán,
Henrik Sandberg
Links: [Conference]
Ongoing work 2: Timing attacks in control loops
Many control systems are subject to computational delays that, sometimes, make the control task miss deadlines (i.e., not produce a new control signal by the time in which new sensor data arrives). Sporadic deadline misses are a common phenomenon, as testified by industry practitioners, and are in general due to a variety of factors, such as transient overloads, hardware problems, and also cyber attacks. Their presence in normally working systems allow an attacker to sneakily introduce them to disrupt the behavior of the closed-loop system without being noticed. In the DYNACON NEST project, we are therefore investigating a class of cyber attacks that target control systems by exploiting timing vulnerabilities, rather than manipulating data.
Our first step was the proposal of an analysis that determines what is the worst case attack that an attacker can do if the defender uses a probabilistic model of how many deadlines the control system is expected to miss. We proposed a Mixed Integer Quadratically Constrained Programming (MIQCP) optimization framework to determine the maximum disruption that an attacker can cause under stealth constraints that stem from an expected probability that the controller will miss its deadline. The attacks are validated on both a simulated quadruple-tank process and a real Furuta pendulum system, showing that even brief, undetected delays can destabilize or degrade system performance significantly.
To ensure the attacks remain stealthy, the optimization problem incorporates statistical constraints based on binomial and geometric distribution tests, mimicking normal system variability and evading detection by standard watchdogs and activity-based intrusion detection systems. We further explored the effectiveness of different defensive strategies, including sliding-window detection and long-term anomaly counters, and evaluates the impact of various parameters such as actuation strategies and deadline miss thresholds. Our study of these attacks concludes by stressing the limitations of current security mechanisms and emphasizing the need for improved detection techniques that consider time-based attacks and long-term behavior patterns.
Researchers: Talitha Nauta,
Henrik Sandberg,
Martina Maggio
Links: [Paper], [Video],
[Code]
Contact
Henrik Sandberg
E-mail: hsan@kth.se
Phone: +46 (0)8 790 7294